Top 5 Gaming Security Encryption Techniques Every Gamer Should Know
In the world of online gaming, ensuring the safety of your data and personal information is paramount. Here are the Top 5 Gaming Security Encryption Techniques every gamer should know:
- End-to-End Encryption: This technique secures data from the point it leaves your device until it reaches the server. It prevents hackers from intercepting sensitive information during transmission.
- SSL/TLS Encryption: Most games utilize SSL (Secure Socket Layer) or TLS (Transport Layer Security) protocols to create a secure connection between your device and the game's server, ensuring that your login credentials and personal data are encrypted and safe.
- Data Masking: This method involves obscuring specific data within a database, replacing it with random characters to protect sensitive information. It helps keep your account details secure even if a breach occurs.
- Two-Factor Authentication (2FA): By requiring a second form of identification, such as a text message code or authentication app verification, 2FA adds an additional layer of security to your gaming accounts.
- Frequent Software Updates: Developers regularly release patches and updates to address security vulnerabilities. Keeping your game clients and devices updated ensures you benefit from the latest encryption techniques designed to protect your gaming experience.
Counter-Strike is a popular first-person shooter game that pits teams of terrorists against counter-terrorists in various mission-based scenarios. Players strategize and communicate to secure objectives, such as bomb defusal or hostage rescue. If you're looking to enhance your gaming experience, consider using a stake promo code for bonuses on gaming platforms.
How to Protect Your Online Gaming Accounts from Cyber Threats
In today's digital age, protecting your online gaming accounts from cyber threats is more crucial than ever. With the rise of advanced hacking techniques, gamers must adopt proactive measures to ensure their accounts remain secure. Start by setting a strong password that includes a mix of letters, numbers, and special characters. Avoid easily guessable information, such as birthdays or common words. Additionally, consider enabling two-factor authentication (2FA) to add an extra layer of security. This requires not only your password but also a verification code, typically sent to your mobile device, making unauthorized access significantly more difficult.
Another essential aspect of account protection is to remain vigilant about phishing attempts. Cybercriminals often use deceptive emails or messages to trick gamers into revealing their login credentials. Always scrutinize the URLs of links you click on, and never provide your account details to anyone who contacts you unsolicited. It's also wise to regularly monitor your account activity for any suspicious actions. By staying informed and implementing these protective measures, you can enhance the security of your online gaming accounts and enjoy a safer gaming experience.
Is Your Game Safe? Understanding the Importance of Encryption in Gaming
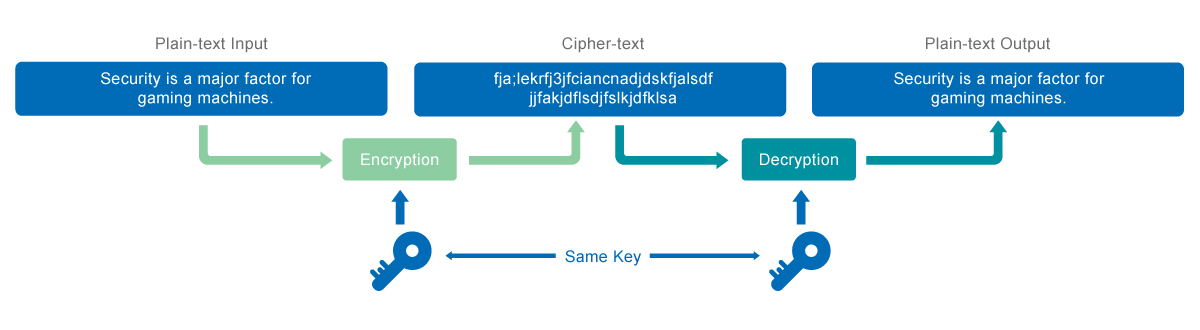
In the digital age, ensuring that your gaming experience is safe and secure is more important than ever. With the rise of online gaming, players are often required to share sensitive information such as personal details and payment methods. This is where encryption plays a crucial role. By encoding this information, encryption protects it from unauthorized access and cyber threats, ensuring that your gaming experience remains enjoyable and secure. For gamers, understanding the importance of encryption can mean the difference between a safe environment and being vulnerable to data breaches.
Moreover, the implementation of strong encryption protocols not only safeguards personal data but also enhances the overall integrity of the game itself. When games use encryption, they minimize the risk of cheating and hacking, providing a fair playing field for all participants. Security measures should include:
- Use of SSL/TLS protocols for secure data transmission
- Regular updates to encryption standards to fend off new cyber threats
- Incorporation of two-factor authentication for user accounts